

Analysts at Moonlock Lab have uncovered a large-scale attack on Web3 developers and crypto specialists. Hackers disguise themselves as venture capitalists and find victims on LinkedIn.
The perpetrators praise the specialists’ projects and propose collaboration. They then send links to fake video conferences that infect computers with viruses.
The Illusion of Legitimate Business
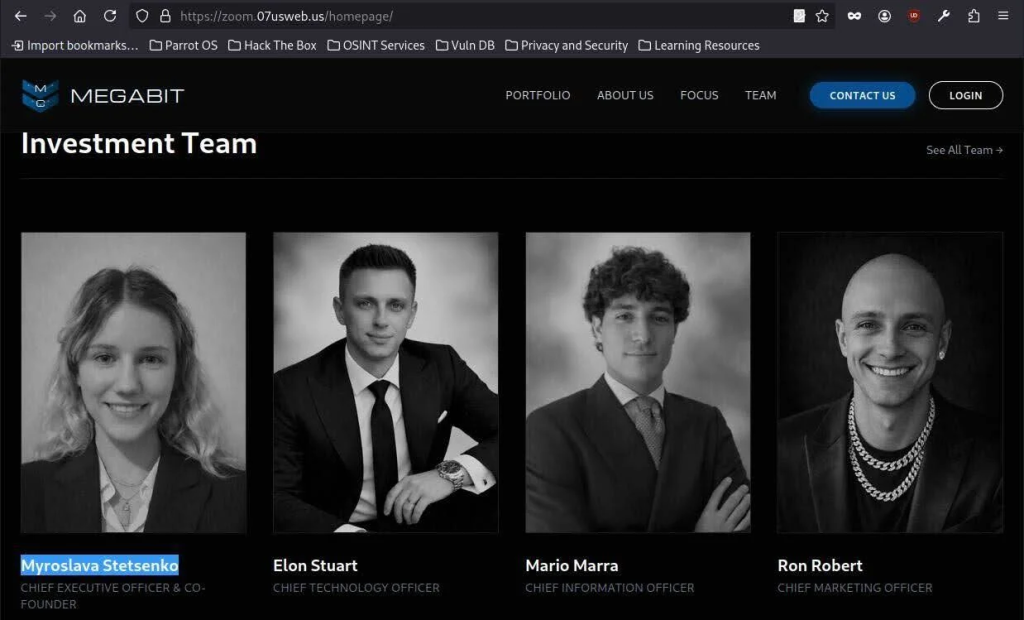
The attackers created three fictitious crypto funds: SolidBit Capital, MegaBit, and Lumax Capital. The websites of these organizations appear credible, featuring corporate history, investment portfolios, and lists of executives. The images of the staff were generated by a neural network.
The fraudsters contact specialists from fake accounts, posing as top managers of these funds. The dialogue begins with compliments on the victim’s professional achievements.
Infection via ClickFix
The attackers quickly move the conversation to messengers and invite the victim to a video call. The victim receives a link to the Calendly service. The address redirects the user to an exact copy of the Zoom, Google Meet, or similar service site.
A Cloudflare verification window pops up on the screen. The system asks the user to check a box to confirm they are not a robot. This is the hacker technique known as ClickFix.
Clicking the button silently copies malicious code to the clipboard. The site displays an animated instruction with a timer, asking the user to open the system terminal, paste the copied text, and press Enter.
The code automatically detects the operating system:
- On Windows, a hidden process runs directly in RAM. The virus does not save files to the hard drive, allowing it to bypass security systems;
- On macOS, the script checks for Python, quietly downloads the necessary libraries, and embeds itself in the system.

In some cases, hackers sent victims an application that fully mimics the interface of the real Zoom on Mac. The program simulates a login window, collects passwords, and sends them to the fraudsters’ Telegram bot.
Links to North Korean Hackers
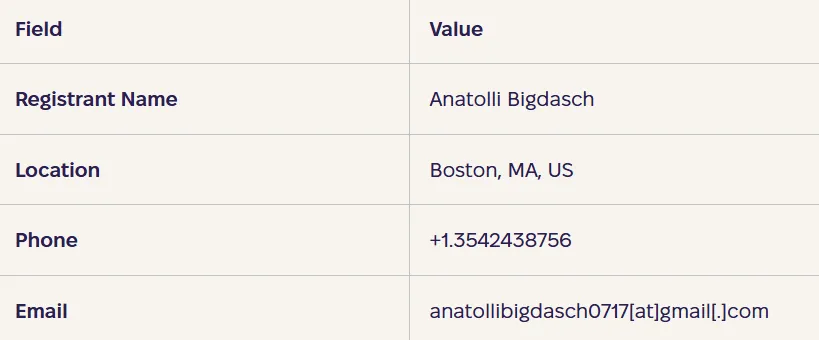
The fake websites’ addresses are registered under the name Anatoly Bigdash from Boston, USA. Experts doubt this person exists.
Researchers noted a similarity in tactics with the methods of the UNC1069 group. This team has been hacking crypto projects since 2018. Analysts at Mandiant previously linked it to North Korea. The criminals use identical structures for malicious links and similar deception scenarios through fake video calls.
To protect against attacks, specialists recommend checking the registration dates of the interlocutors’ domains. Legitimate services never ask users to enter commands in the terminal to verify identity or start a broadcast. The deception can be detected at the stage of clicking on external links.
Back in June 2025, investment partner Mehdi Farooq of the venture firm Hypersphere fell victim to a phishing attack via a fake Zoom call.









